| Question.91 A forensic expert working on a fraud investigation for a US-based company collected a few disk images as evidence. Which of the following offers an authoritative decision about whether the evidence was obtained legally? (A) Lawyers (B) Court (C) Upper management team (D) Police |
91. Click here to View Answer
Answer: A
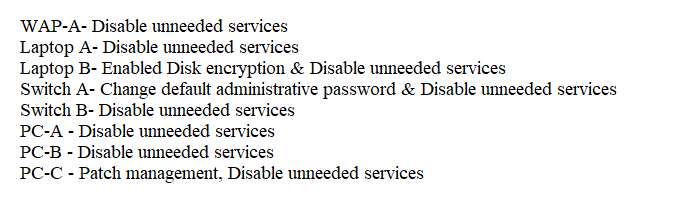
| Question.92 SIMULATION A security engineer needs to review the configurations of several devices on the network to meet the following requirements: The PostgreSQL server must only allow connectivity in the 10.1.2.0/24 subnet. The SSH daemon on the database server must be configured to listen to port 4022. The SSH daemon must only accept connections from a single workstation. All host-based firewalls must be disabled on all workstations. All devices must have the latest updates from within the past eight days. All HDDs must be configured to secure data at rest. Cleartext services are not allowed. All devices must be hardened when possible. INSTRUCTIONS Click on the various workstations and network devices to review the posture assessment results. Remediate any possible issues or indicate that no issue is found. Click on Server A to review output data. Select commands in the appropriate tab to remediate connectivity problems to the PostgreSQL database via SSH. If at any time you would like to bring back the initial state of the simulation, please click the Reset All button. 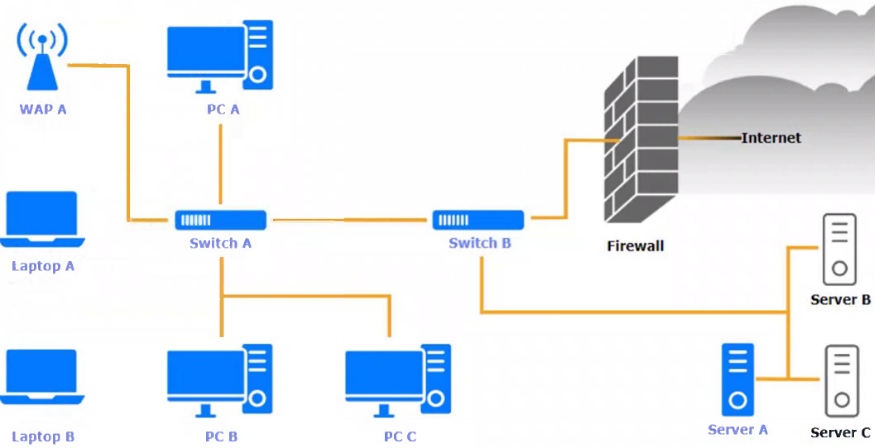 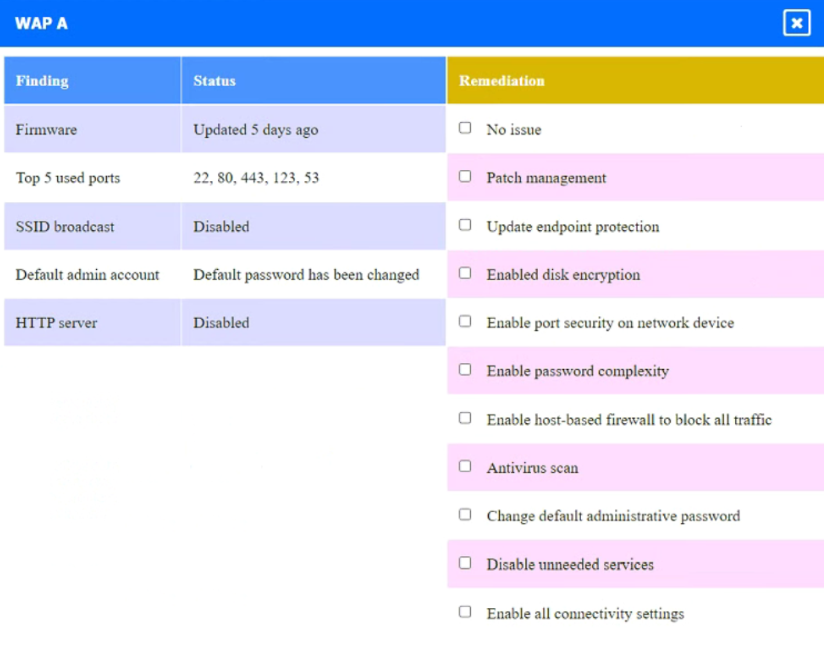 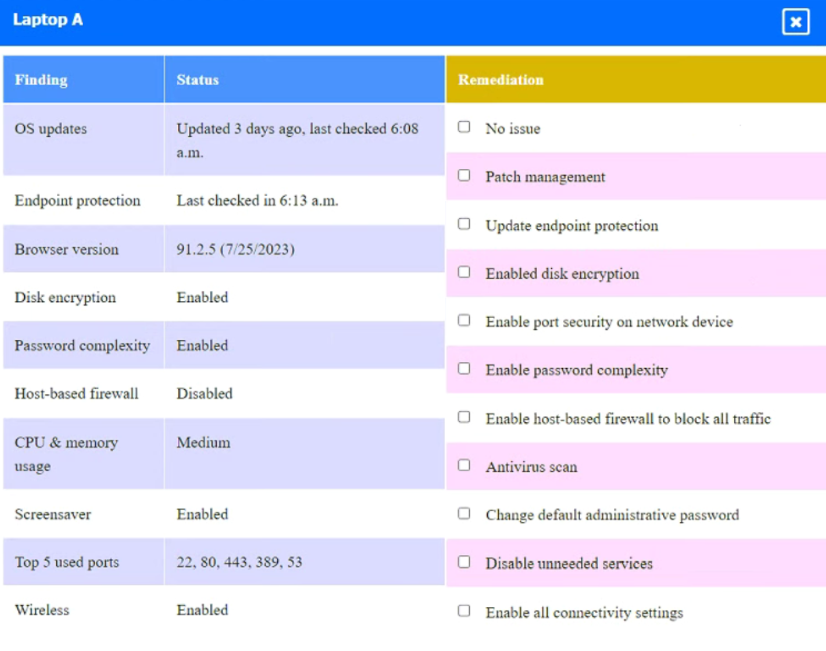 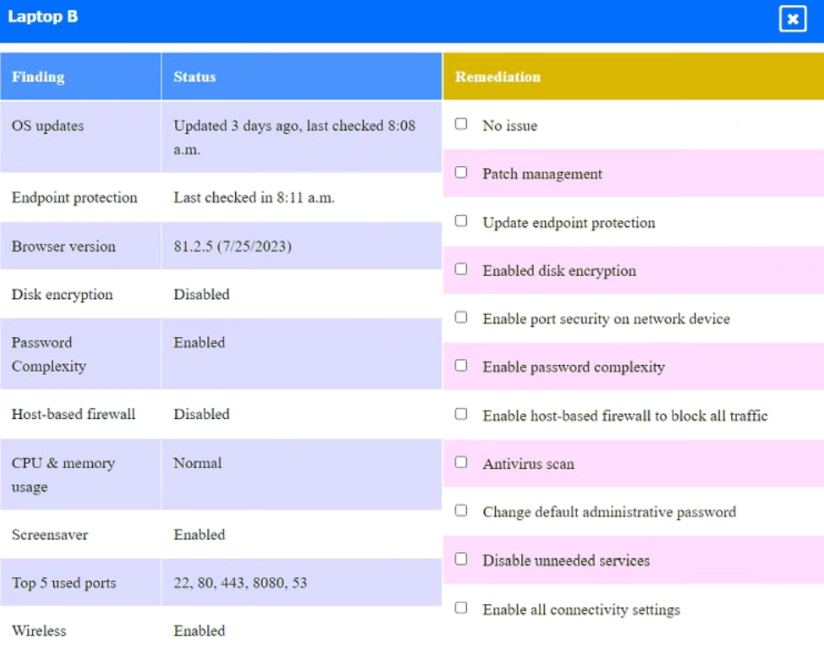 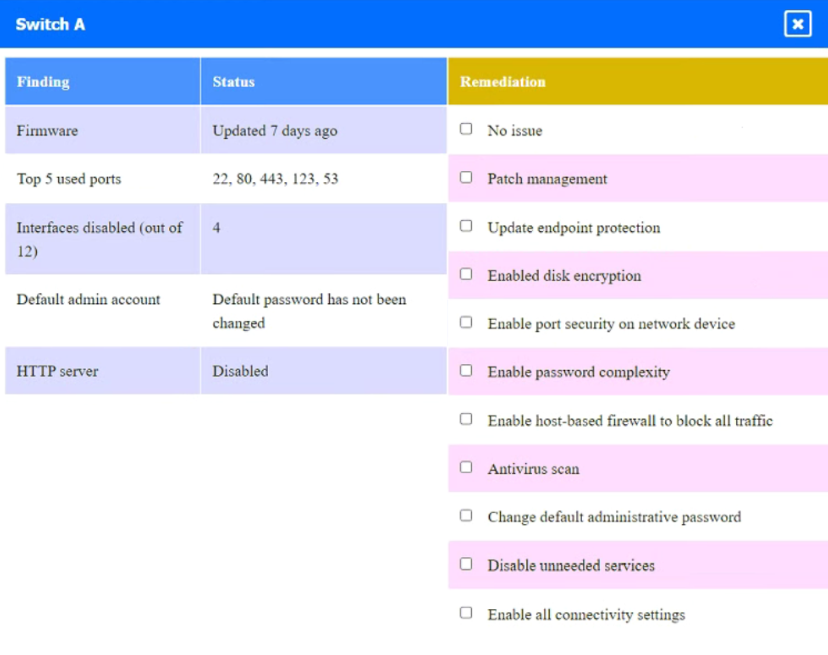 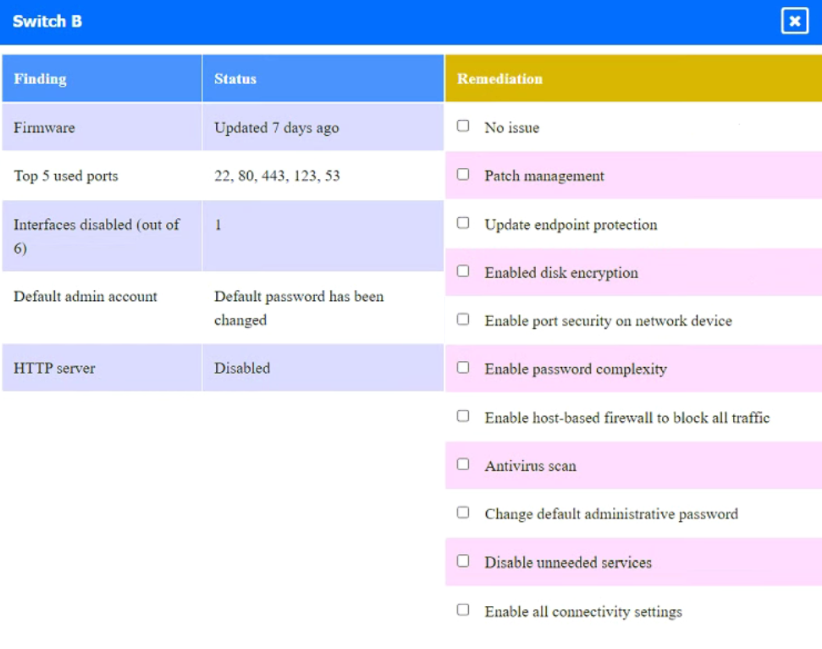  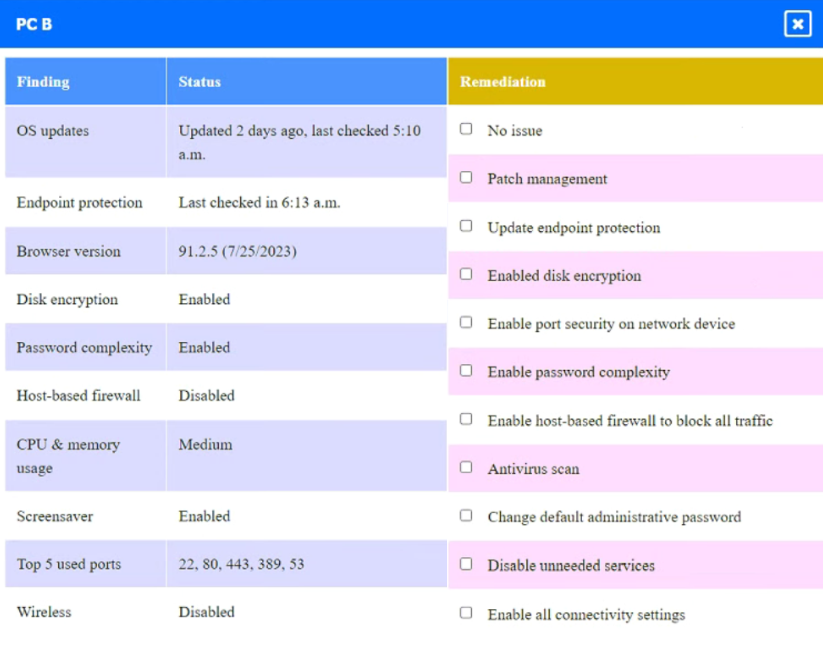 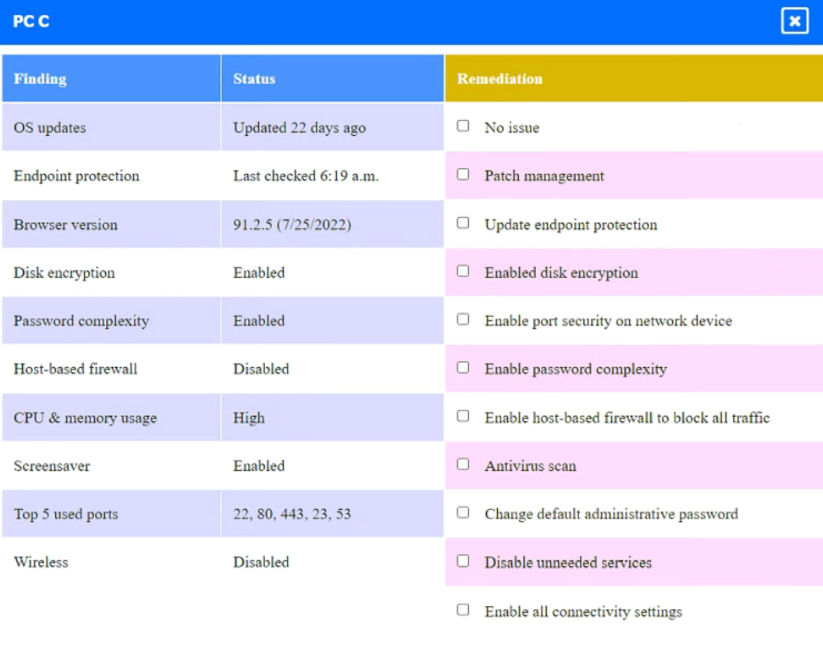 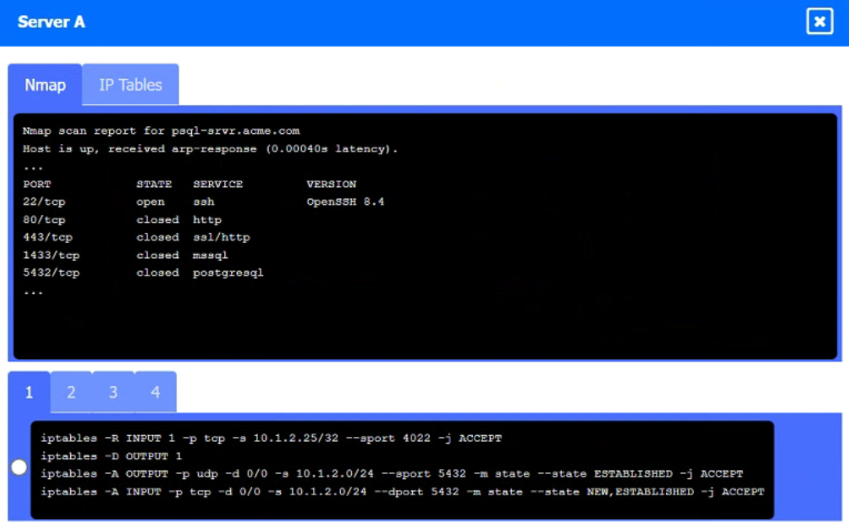 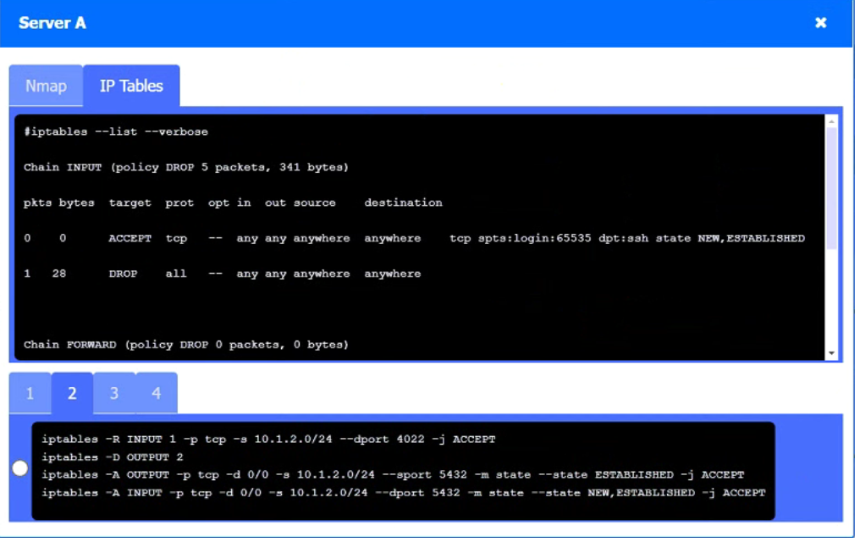 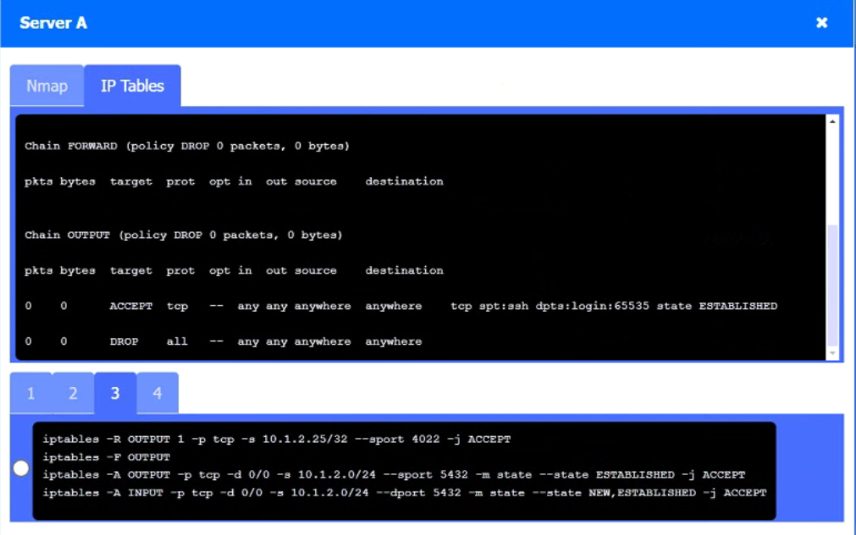 |
92. Click here to View Answer
Answer:
| Question.93 A security consultant needs to protect a network of electrical relays that are used for monitoring and controlling the energy used in a manufacturing facility. Which of the following systems should the consultant review before making a recommendation? (A) CAN (B) ASIC (C) FPGA (D) SCADA |
93. Click here to View Answer
Answer: D
| Question.94 A review of the past year’s attack patterns shows that attackers stopped reconnaissance after finding a susceptible system to compromise. The company would like to find a way to use this information to protect the environment while still gaining valuable attack information. Which of the following would be BEST for the company to implement? (A) A WAF (B) An IDS (C) A SIEM (D) A honeypot |
94. Click here to View Answer
Answer: D
| Question.95 A disaster recovery team learned of several mistakes that were made during the last disaster recovery parallel test. Computational resources ran out at 70% of restoration of critical services. Which of the following should be modified to prevent the issue from reoccurring? (A) Recovery point objective (B) Recovery time objective (C) Mission-essential functions (D) Recovery service level |
95. Click here to View Answer
Answer: D
Reference:
https://www.nakivo.com/blog/disaster-recovery-in-cloud-computing/