| Question.26 A software assurance analyst reviews an SSH daemons source code and sees the following: 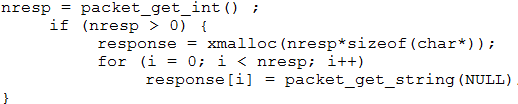 Based on this code snippet, which of the following attacks is MOST likely to succeed? (A) Race condition (B) Cross-site scripting (C) Integer overflow (D) Driver shimming |
26. Click here to View Answer
Answer: C
| Question.27 Real-time, safety-critical systems MOST often use serial busses that: (A) have non-deterministic behavior and are not deployed with encryption. (B) have non-deterministic behavior and are deployed with encryption. (C) have deterministic behavior and are deployed with encryption. (D) have deterministic behavior and are not deployed with encryption. |
27. Click here to View Answer
Answer: C
| Question.28 A security analyst discovered that the company’s WAF was not properly configured. The main web server was breached, and the following payload was found in one of the malicious requests: 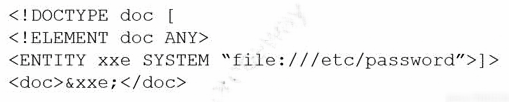 Which of the following would BEST mitigate this vulnerability? (A) CAPTCHA (B) Input validation (C) Data encoding (D) Network intrusion prevention |
28. Click here to View Answer
Answer: B
| Question.29 Which of the following is used to assess compliance with internal and external requirements? (A) RACI matrix (B) Audit report (C) After-action report (D) Business continuity plan |
29. Click here to View Answer
Answer: B
| Question.30 A cybersecurity analyst discovered a private key that could have been exposed. Which of the following is the BEST way for the analyst to determine if the key has been compromised? (A) HSTS (B) CRL (C) CSRs (D) OCSP |
30. Click here to View Answer
Answer: C