| Question. 41 You are in the process of configuring an Azure policy via the Azure portal. Your policy will include an effect that will need a managed identity for it to be assigned. Which of the following is the effect in question? A. AuditIfNotExist B. Disabled C. DeployIfNotExist D. EnforceOPAConstraint |
41. Click here to View Answer
Answer:
C
Explanation:
When Azure Policy runs the template in the deployIfNotExists policy definition, it does so using a managed identity.
Reference:
https://docs.microsoft.com/bs-latn-ba/azure/governance/policy/how-to/remediate-resources
| Question. 42 You have been tasked with creating an Azure key vault using PowerShell. You have been informed that objects deleted from the key vault must be kept for a set period of 90 days. Which two of the following parameters must be used in conjunction to meet the requirement? (Choose two.) A. EnabledForDeployment B. EnablePurgeProtection C. EnabledForTemplateDeployment D. EnableSoftDelete |
42. Click here to View Answer
Answer:
BD
Explanation:
– EnablePurgeProtection an EnableSoftDelete
Reference:
https://docs.microsoft.com/en-us/powershell/module/azurerm.keyvault/new-azurermkeyvault https://docs.microsoft.com/en-us/azure/key-vault/key-vault-ovw-soft-delete
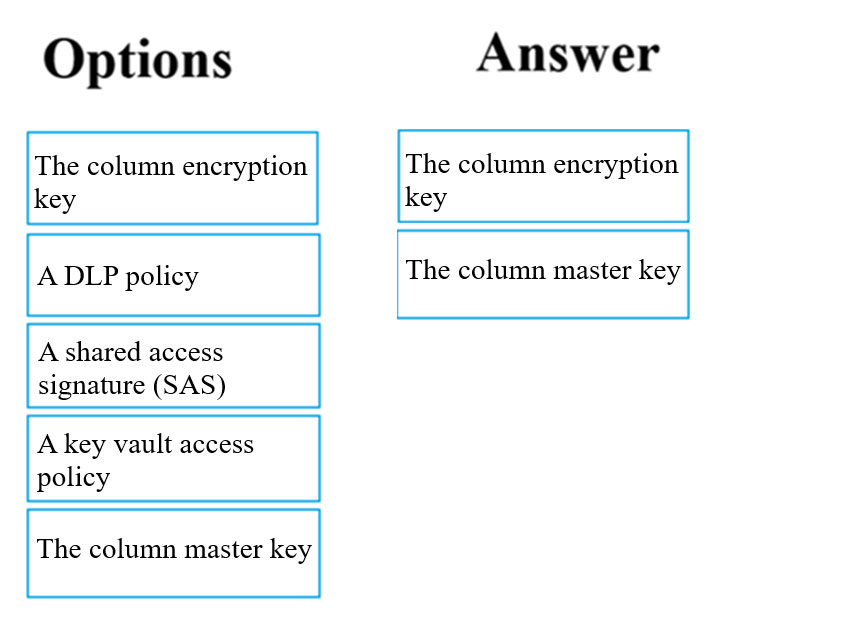
| Question. 43 DRAG DROP – Your company has an Azure SQL database that has Always Encrypted enabled. You are required to make the relevant information available to application developers to allow them to access data in the database. Which two of the following options should be made available? Answer by dragging the correct options from the list to the answer area. Select and Place: 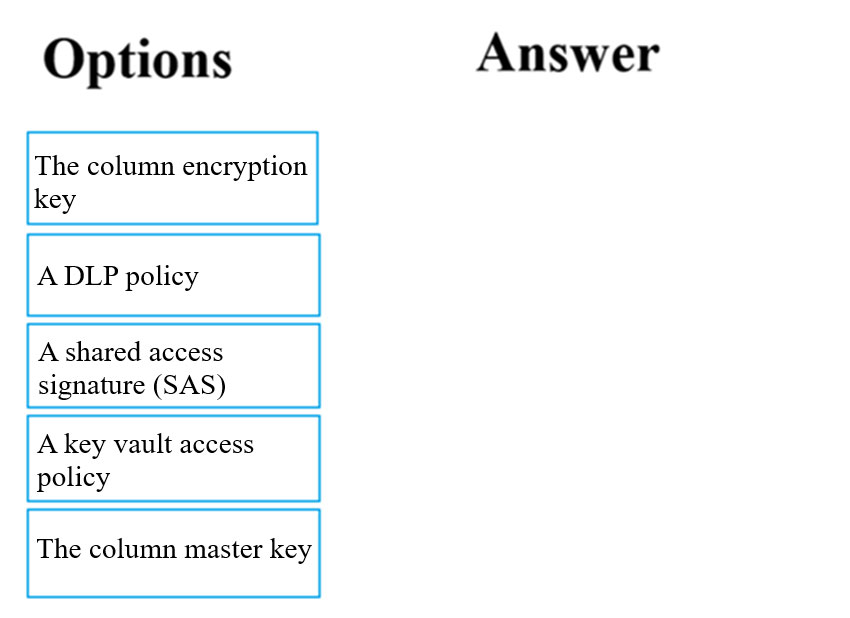 |
43. Click here to View Answer
Answer:
Explanation:
Always Encrypted uses two types of keys: column encryption keys and column master keys. A column encryption key is used to encrypt data in an encrypted column. A column master key is a key-protecting key that encrypts one or more column encryption keys.
| Question. 44 Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You have an Azure subscription named Sub1. You have an Azure Storage account named sa1 in a resource group named RG1. Users and applications access the blob service and the file service in sa1 by using several shared access signatures (SASs) and stored access policies. You discover that unauthorized users accessed both the file service and the blob service. You need to revoke all access to sa1. Solution: You create a new stored access policy. Does this meet the goal? A. Yes B. No |
44. Click here to View Answer
Answer:
B
Explanation:
Creating a new (additional) stored access policy with have no effect on the existing policy or the SAS’s linked to it.
To revoke a stored access policy, you can either delete it, or rename it by changing the signed identifier. Changing the signed identifier breaks the associations between any existing signatures and the stored access policy. Deleting or renaming the stored access policy immediately effects all of the shared access signatures associated with it.
Reference:
https://docs.microsoft.com/en-us/rest/api/storageservices/Establishing-a-Stored-Access-Policy
| Question. 45 Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution. After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen. You have a hybrid configuration of Azure Active Directory (Azure AD). You have an Azure HDInsight cluster on a virtual network. You plan to allow users to authenticate to the cluster by using their on-premises Active Directory credentials. You need to configure the environment to support the planned authentication. Solution: You deploy the On-premises data gateway to the on-premises network. Does this meet the goal? A. Yes B. No |
45. Click here to View Answer
Answer:
B
Explanation:
Instead, you connect HDInsight to your on-premises network by using Azure Virtual Networks and a VPN gateway.
Note: To allow HDInsight and resources in the joined network to communicate by name, you must perform the following actions:
✑ Create Azure Virtual Network.
✑ Create a custom DNS server in the Azure Virtual Network.
✑ Configure the virtual network to use the custom DNS server instead of the default Azure Recursive Resolver.
✑ Configure forwarding between the custom DNS server and your on-premises DNS server.
Reference:
https://docs.microsoft.com/en-us/azure/hdinsight/connect-on-premises-network